To write a file from a Python string directly to an S3 bucket we need to use the boto3 package.
There are 2 ways to write a file in S3 using boto3. The first is via the boto3 client, and the second is via the boto3 resource. Both of these methods will be shown below.
- S3 object and keys definition
- Writing S3 objects using boto3 resource
- Writing S3 objects using boto3 client
- Lambda Function to write S3 objects
- String-to-bytes conversion
S3 objects and keys
If you are new to AWS S3, you might be confused with some of the terms. So we’ll define some of them here. If you already know what objects and keys are then you can skip this section.
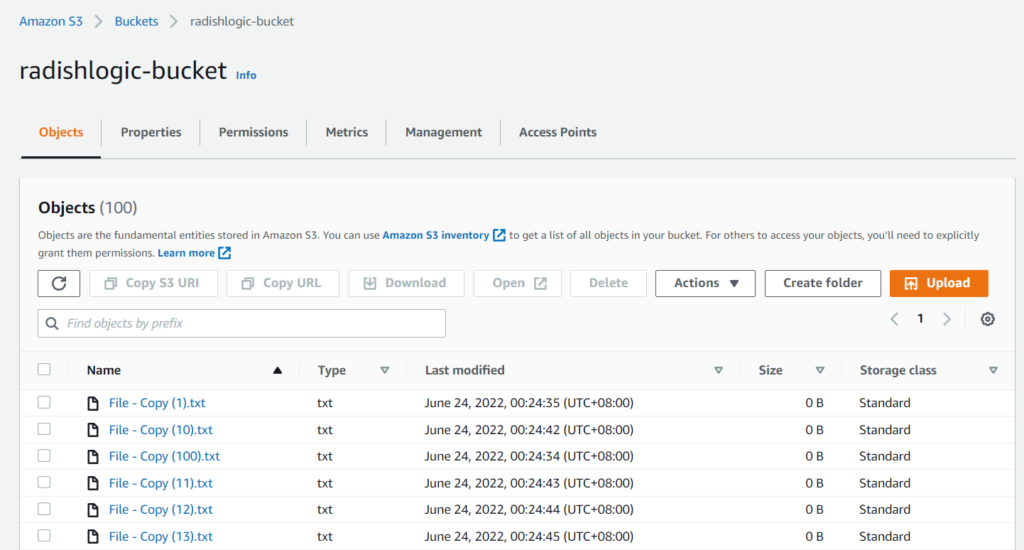
S3 objects are the same as files. When we run the method put_object what it means is that we are putting a file into S3.
S3 keys are the same as the filename with its full path. So if we want to create an object in S3 with the name of filename.txt within the foobar folder then the key is foobar/filename.txt.
Now that we have clarified some of the AWS S3 terms, follow the details below to start writing Python strings directly to objects in S3.
Continue reading How to write Python string to a file in S3 Bucket using boto3